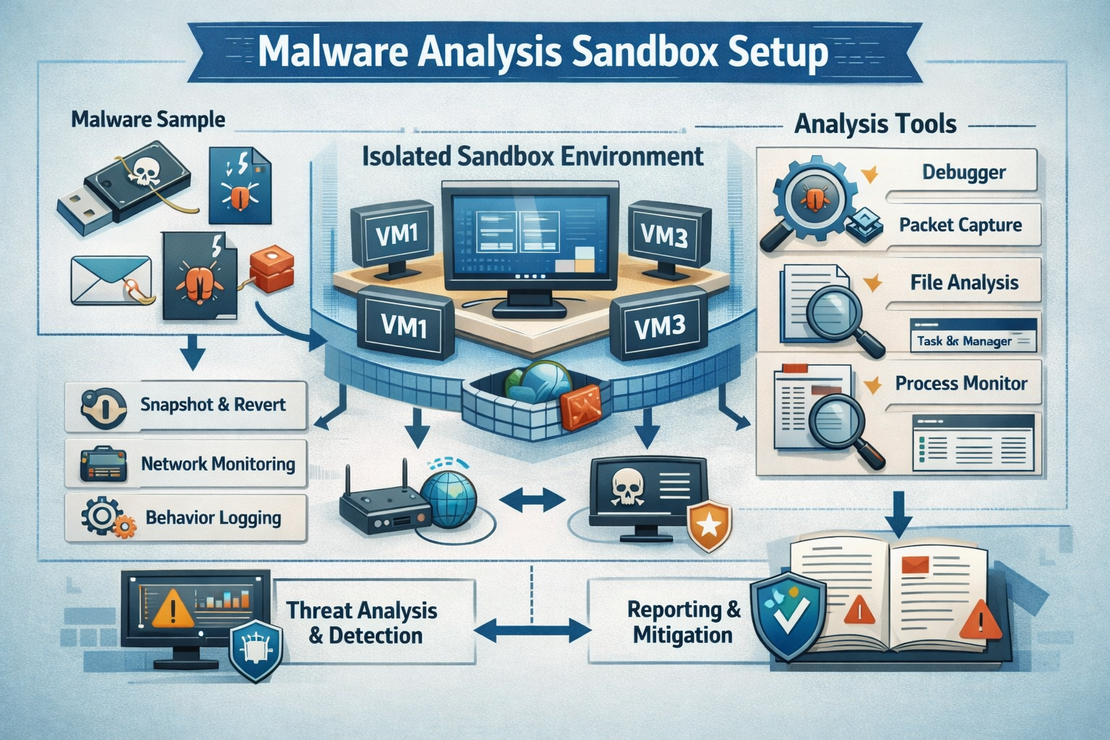
Malware Analysis Sandbox Setup
Overview Build a secure malware analysis environment for SOC Analysts to safely analyze malicious samples and extract threat intelligence.
Read More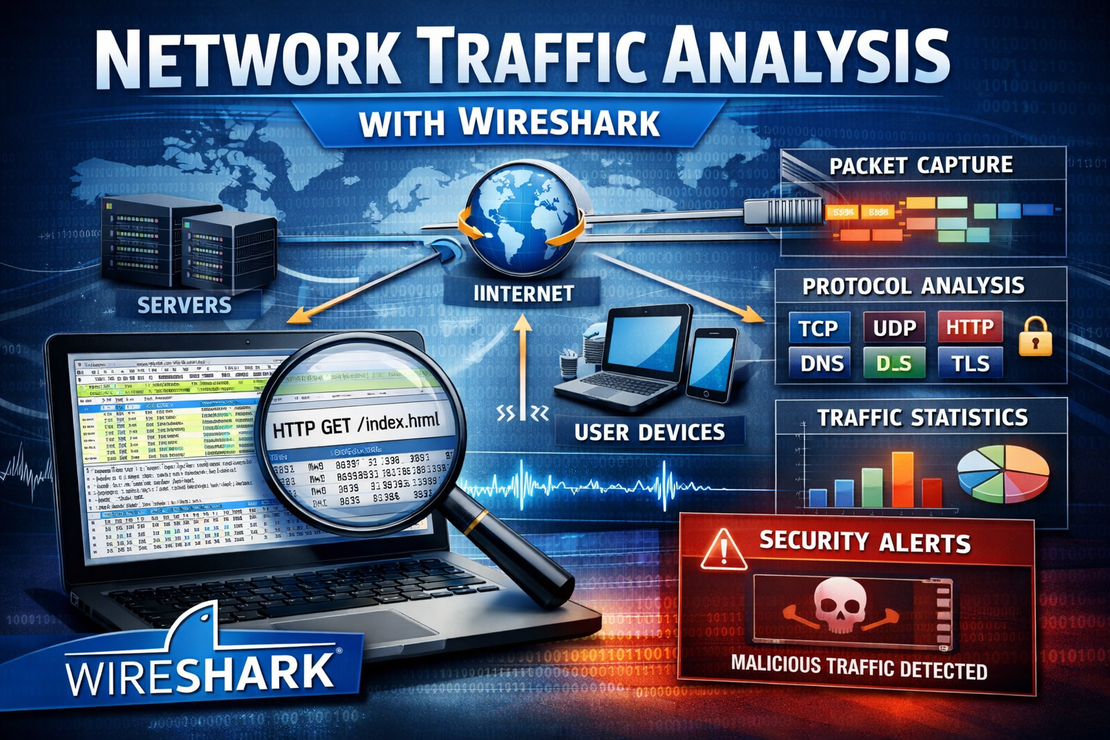
Network Traffic Analysis with Wireshark
Overview A comprehensive SOC Analyst project for analyzing network traffic to detect security threats and understand attack patterns using Wireshark.
Read More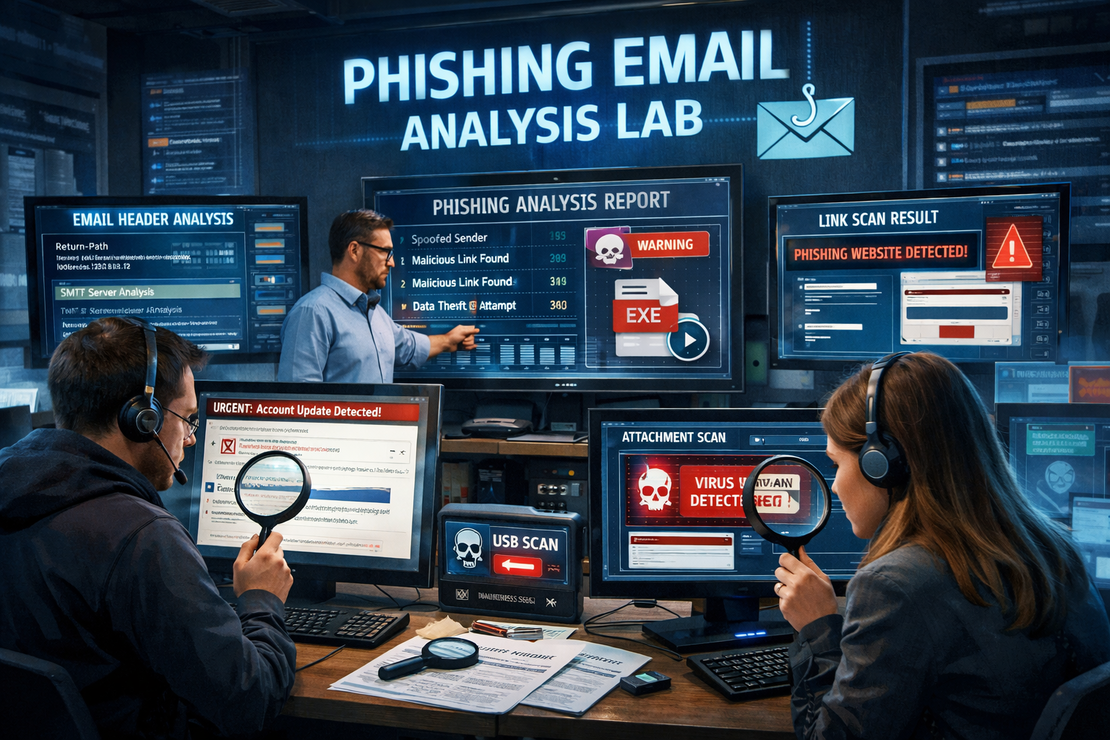
Phishing Email Analysis Lab
Overview A comprehensive SOC Analyst project for analyzing phishing emails and developing incident response skills.
Read More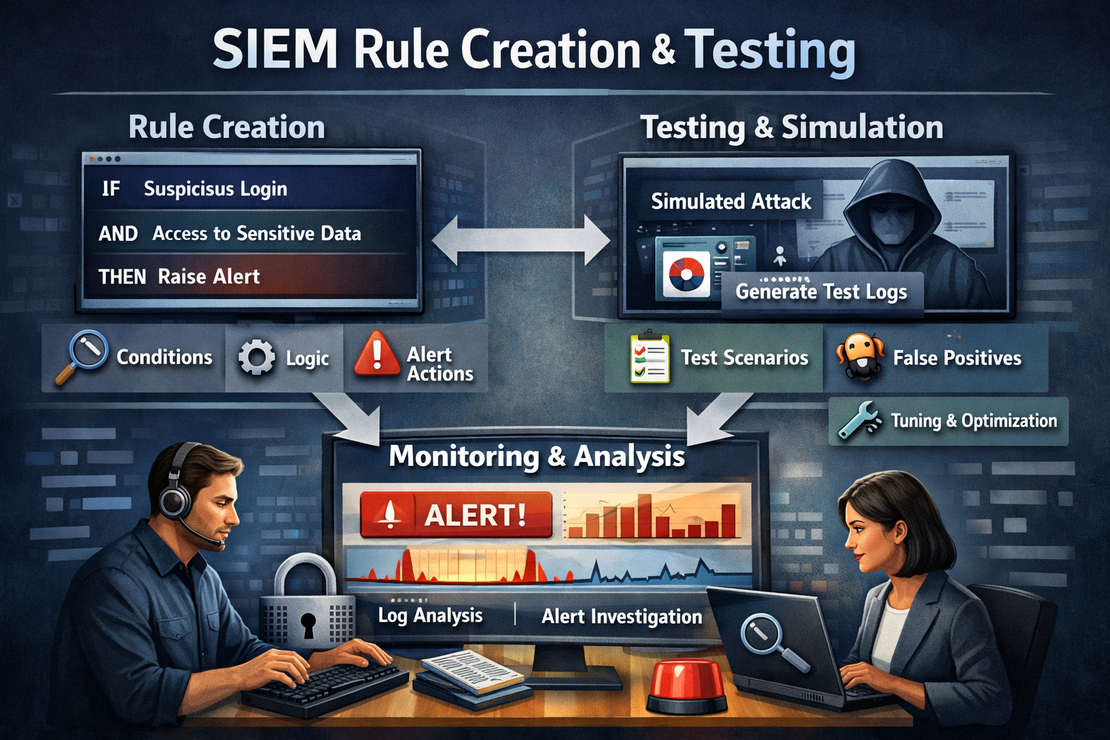
SIEM Rule Creation and Testing
Overview Develop and test SIEM detection rules to enhance SOC monitoring capabilities and improve threat detection across multiple attack vectors.
Read More
SOC Analyst Projects
Welcome to a comprehensive collection of hands-on SOC Analyst projects designed to build practical cybersecurity skills.
Read More
Windows Log Forensics Investigation
Overview A hands-on SOC Analyst project for investigating Windows security events and detecting potential intrusions using system logs.
Read More
Certificates
Cisco Networking Academy Free online courses. In-person learning. Certification-aligned pathways in topics like Cybersecurity, Networking, and Python.
Read More
Advent of Cyber 2025 Recap: Shells, Phishing, and Splunk
🎄 Advent of Cyber 2025: Days 1-4 Here’s a look at the first few days of TryHackMe’s Advent of Cyber event, covering essential topics in cybersecurity.
Read MoreJoin Me for Advent of Cyber 2025!
I am excited to announce that I will be participating in Advent of Cyber 2025 hosted by TryHackMe!
Read More
Cyber security🔒
Tools Bitwarden Bitwarden is a free and open-source password manager that helps users securely store and manage their login credentials, encryption keys, and other sensitive data. It offers advanced security features, including end-to-end encryption, two-factor authentication, and zero-knowledge proof, ensuring that only the user has access to their stored information
Read More