Windows Log Forensics Investigation
- Jean-Christophe Miler
- Soc , Cybersecurity
- February 12, 2026
Table of Contents
Overview
A hands-on SOC Analyst project for investigating Windows security events and detecting potential intrusions using system logs.
Learning Objectives
- Analyze Windows Event Logs for security incidents
- Identify patterns of malicious activity
- Correlate events across different log sources
- Build timeline of security events
- Document forensic findings
Project Structure
windows-log-forensics/
├── sample-logs/
│ ├── security.evtx
│ ├── system.evtx
│ ├── application.evtx
│ └── powershell.evtx
├── analysis-scripts/
│ ├── event-parser.py
│ ├── timeline-builder.py
│ └── anomaly-detector.py
├── tools/
│ ├── evtx-dump.py
│ └── log-parser.py
├── documentation/
│ ├── windows-event-id-reference.md
│ └── investigation-checklist.md
├── reports/
│ └── forensic-analysis-template.md
└── README.md
Tools Required
- Windows Event Viewer
- Python 3.8+ with
evtxlibrary - Velociraptor or Hayabusa for log analysis
- Timeline analysis tools
- Splunk/ELK stack (Optional)
Investigation Scenarios
Scenario 1: Suspicious Logon Activity
- Analyze failed login attempts (Event ID 4625)
- Identify potential brute force attacks
- Detect lateral movement (Event ID 4624, Logon Type 3)
- Track unusual authentication patterns
Scenario 2: Malicious Process Execution
- Investigate suspicious process creation (Event ID 4688)
- Analyze PowerShell script blocks (Event ID 4104)
- Detect potential living-off-the-land techniques
- Identify process injection attempts
Scenario 3: Privilege Escalation Attempts
- Monitor for unusual privilege changes (Event ID 4670)
- Analyze service creation/modification (Event ID 7045)
- Detect scheduled task creation (Event ID 4698)
- Investigate registry modifications
Key Event IDs to Monitor
Authentication Events
- 4624: Account logon successful
- 4625: Account logon failed
- 4634: Account logoff
- 4648: Explicit credentials used
- 4768/4769: Kerberos authentication
Process Events
- 4688: New process created
- 4689: Process ended
- 4656/4663: Object access
- 4103/4104: PowerShell script block logging
System Events
- 7045: New service installed
- 4698: Scheduled task created
- 4670: Permissions changed on object
Sample Analysis Scripts
Event Log Parser
import evtx
import xml.etree.ElementTree as ET
from datetime import datetime
def parse_security_events(evtx_file, event_ids=None):
"""
Parse Windows Security Event Log
"""
events = []
with evtx.Evtx(evtx_file) as log:
for record in log.records():
xml = record.xml()
root = ET.fromstring(xml)
event_id = root.find('.//EventID').text
if event_ids and event_id not in event_ids:
continue
timestamp = root.find('.//System/TimeCreated').get('SystemTime')
timestamp = datetime.fromisoformat(timestamp.replace('Z', '+00:00'))
event_data = {}
for data in root.findall('.//EventData/Data'):
name = data.get('Name')
event_data[name] = data.text
events.append({
'timestamp': timestamp,
'event_id': event_id,
'data': event_data
})
return events
def detect_brute_force(events, threshold=10, time_window=300):
"""
Detect potential brute force attacks
"""
failed_logins = [e for e in events if e['event_id'] == '4625']
attacks = []
for i, event in enumerate(failed_logins):
window_events = []
for later_event in failed_logins[i:]:
time_diff = (later_event['timestamp'] - event['timestamp']).total_seconds()
if time_diff <= time_window:
window_events.append(later_event)
else:
break
if len(window_events) >= threshold:
attacks.append({
'start_time': event['timestamp'],
'count': len(window_events),
'target_account': event['data'].get('TargetUserName'),
'source_ip': event['data'].get('IpAddress')
})
return attacks
Timeline Builder
import pandas as pd
from datetime import datetime, timedelta
def build_incident_timeline(events, start_time, end_time):
"""
Build a timeline of security events
"""
timeline = []
for event in events:
event_time = event['timestamp']
if start_time <= event_time <= end_time:
timeline.append({
'timestamp': event_time,
'event_id': event['event_id'],
'description': get_event_description(event),
'severity': get_event_severity(event['event_id']),
'details': event['data']
})
return sorted(timeline, key=lambda x: x['timestamp'])
def get_event_description(event):
"""Generate human-readable event description"""
event_id = event['event_id']
data = event['data']
descriptions = {
'4625': f"Failed logon for {data.get('TargetUserName')} from {data.get('IpAddress')}",
'4624': f"Successful logon for {data.get('TargetUserName')} from {data.get('IpAddress')}",
'4688': f"Process created: {data.get('NewProcessName')} by {data.get('SubjectUserName')}",
'4104': f"PowerShell script executed by {data.get('UserId')}"
}
return descriptions.get(event_id, f"Event {event_id} occurred")
Investigation Steps
1. Initial Assessment
- Collect relevant log files
- Determine time window for investigation
- Identify critical systems and users
- Establish baseline activity
2. Event Correlation
- Correlate authentication events with process creation
- Link network connections to application events
- Identify sequences of suspicious activities
- Build attack chain timeline
3. Anomaly Detection
- Identify unusual login times/locations
- Detect privilege escalation attempts
- Find suspicious process executions
- Flag unauthorized system changes
4. Impact Assessment
- Determine affected accounts and systems
- Assess data access and exfiltration risks
- Identify persistence mechanisms
- Evaluate business impact
5. Documentation
- Create detailed timeline of events
- Document all findings and evidence
- Provide remediation recommendations
- Update detection rules
Sample Investigation Findings
Brute Force Attack Detection
Timeline:
2026-02-12 08:00:15 - Failed logon attempt for admin (192.168.1.100)
2026-02-12 08:00:16 - Failed logon attempt for admin (192.168.1.100)
[... 15 more failed attempts ...]
2026-02-12 08:05:22 - Successful logon for admin (192.168.1.100)
Findings:
- 16 failed attempts followed by successful login
- Source IP: 192.168.1.100
- Target: Administrator account
- Indicates potential credential compromise
PowerShell Malicious Activity
Events Detected:
2026-02-12 09:15:30 - PowerShell script block executed (EncodedCommand)
2026-02-12 09:15:31 - Process created: powershell.exe (Base64 encoded payload)
2026-02-12 09:15:32 - Network connection to 185.14.28.45:443
Analysis:
- Encoded PowerShell commands detected
- Suspicious network activity following execution
- Potential malware download/execution
Expected Deliverables
- Completed forensic analysis report
- Event timeline with annotations
- IOC list from log analysis
- Detection rule recommendations
- Blog post documenting investigation process
Extension Ideas
- Automated log analysis pipeline
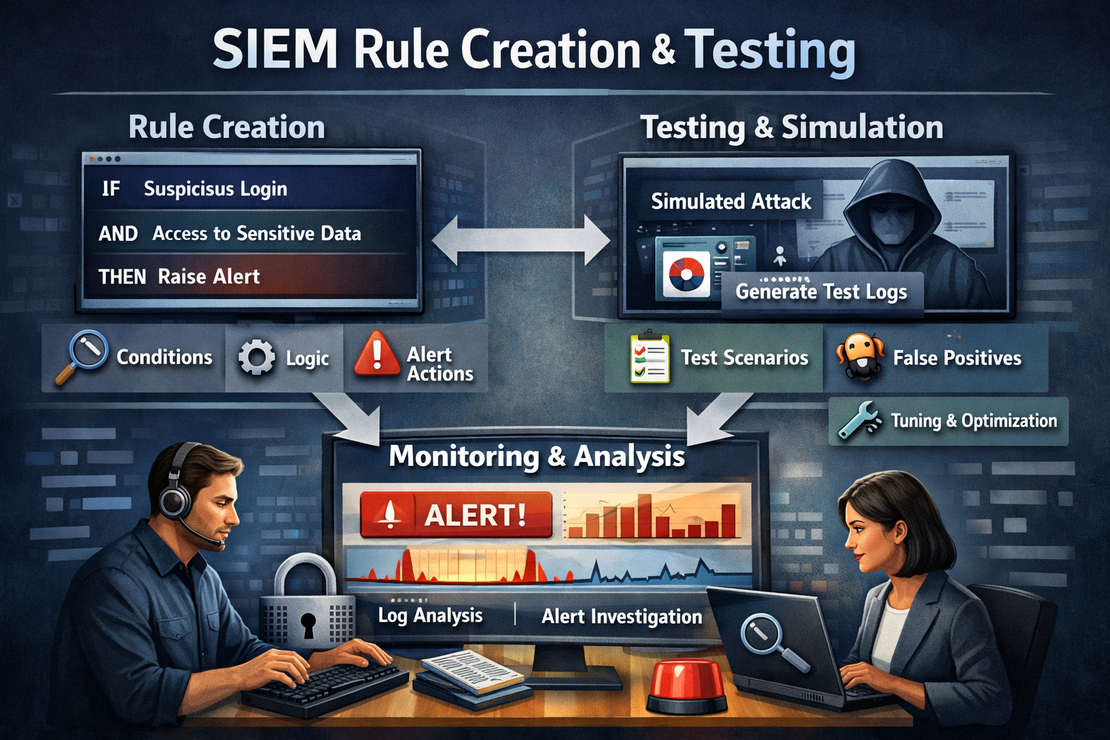
- Integration with SIEM for real-time detection
- Machine learning model for anomaly detection
- Custom dashboard for security monitoring
Resources
Safety Notes
- Work with sanitized log data for training
- Follow chain of custody procedures for real incidents
- Document all analysis steps
- Validate findings with multiple sources