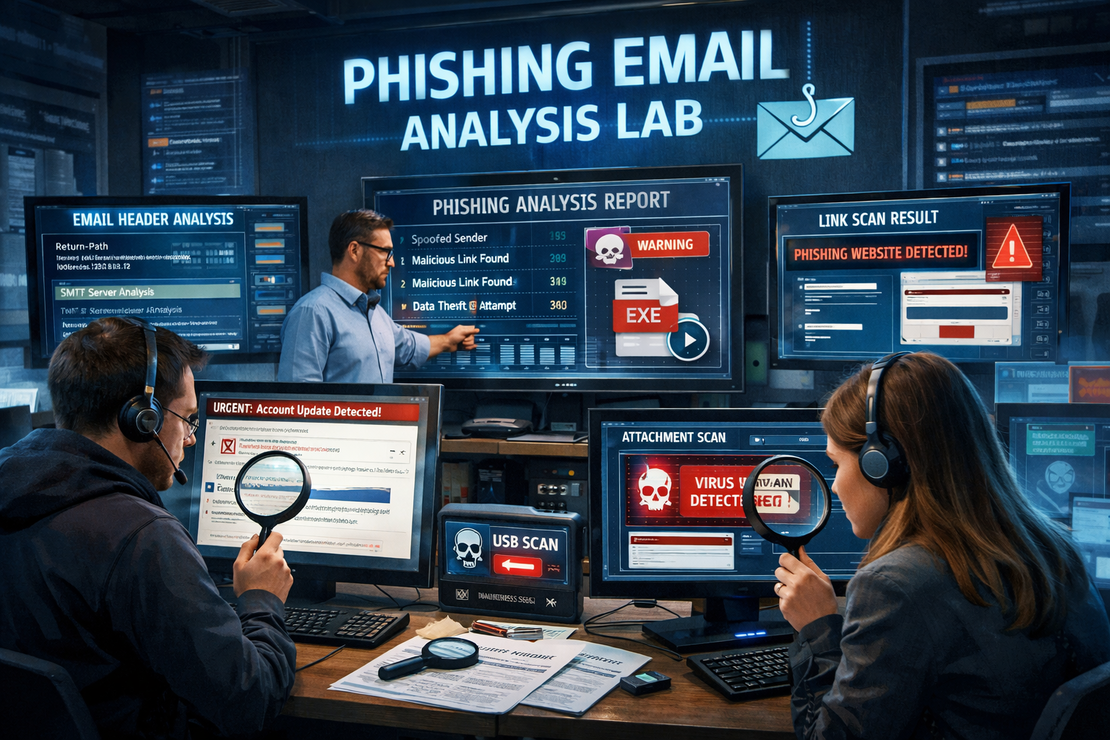
Phishing Email Analysis Lab
- Jean-Christophe Miler
- Soc , Cybersecurity
- February 12, 2026
Table of Contents
Overview
A comprehensive SOC Analyst project for analyzing phishing emails and developing incident response skills.
Learning Objectives
- Identify phishing email indicators
- Extract and analyze email headers
- Analyze malicious attachments safely
- Document findings in SOC ticket format
Project Structure
phishing-analysis-lab/
├── sample-emails/
│ ├── phishing1.eml
│ ├── phishing2.eml
│ └── legitimate.eml
├── analysis-tools/
│ ├── email-header-parser.py
│ ├── indicator-extractor.py
│ └── report-generator.py
├── documentation/
│ ├── analysis-checklist.md
│ └── incident-response-playbook.md
├── reports/
│ └── analysis-report-template.md
└── README.md
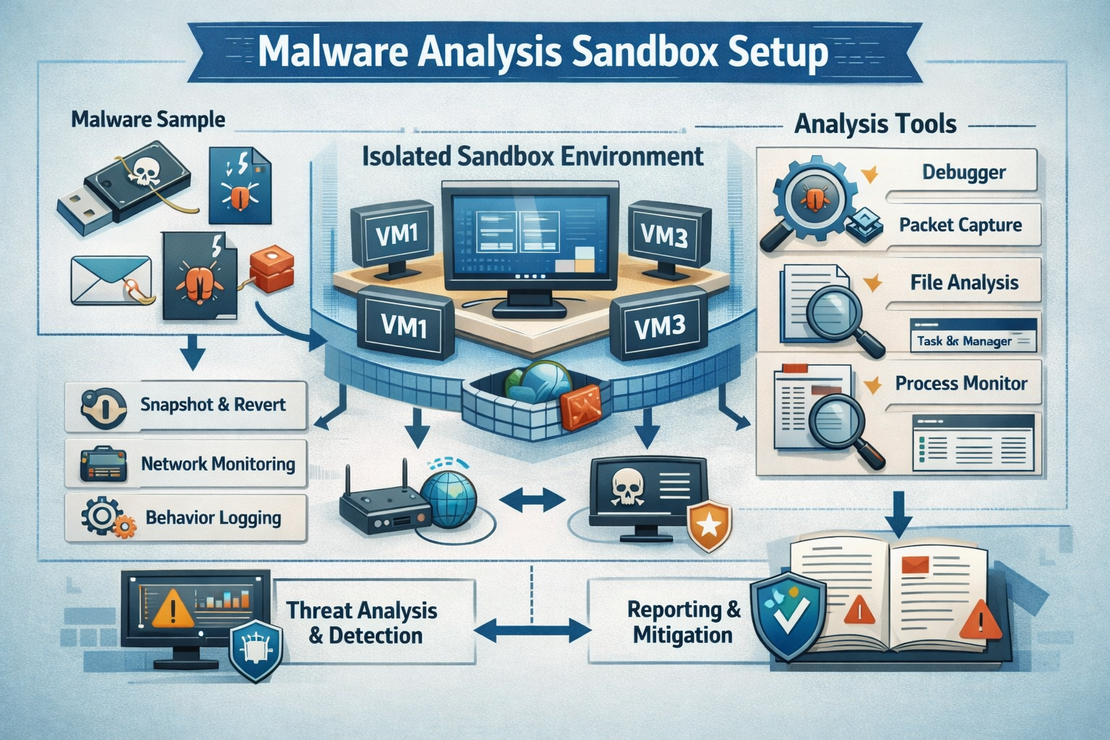
Tools Required
- Python 3.8+
- Email analysis tools (Thunderbird, Outlook)
- VirusTotal API
- YARA rules
- Sandbox environment (Optional)
Steps to Complete
1. Email Header Analysis
- Extract email headers from sample .eml files
- Analyze Received: headers for routing anomalies
- Check SPF, DKIM, DMARC validation
- Identify spoofing attempts
2. Content Analysis
- Examine email body for social engineering tactics
- Identify urgency cues and pressure techniques
- Analyze link URLs using URL decoding tools
- Check for credential harvesting indicators
3. Attachment Analysis
- Safely extract attachments in isolated environment
- Calculate file hashes (MD5, SHA256)
- Submit to VirusTotal for analysis
- Analyze with YARA rules if malicious
4. IOC Extraction
- Extract malicious IP addresses
- Identify suspicious domains/URLs
- Document email addresses and subjects
- Create threat intelligence feeds
5. Reporting
- Complete analysis report using template
- Create executive summary
- Provide remediation recommendations
- Document lessons learned
Sample Code Snippets
Email Header Parser
import email
from email.header import decode_header
def parse_email_headers(eml_file):
with open(eml_file, 'r') as f:
msg = email.message_from_file(f)
headers = {}
for key, value in msg.items():
decoded_value = decode_header(value)[0][0]
if isinstance(decoded_value, bytes):
decoded_value = decoded_value.decode('utf-8', errors='ignore')
headers[key] = decoded_value
return headers
IOC Extractor
import re
import hashlib
def extract_iocs(email_content):
iocs = {
'ips': [],
'urls': [],
'domains': [],
'email_addresses': []
}
# IP Address pattern
ip_pattern = r'\b(?:[0-9]{1,3}\.){3}[0-9]{1,3}\b'
iocs['ips'] = list(set(re.findall(ip_pattern, email_content)))
# URL pattern
url_pattern = r'https?://[^\s<>"{}|\\^`\[\]]+'
iocs['urls'] = list(set(re.findall(url_pattern, email_content)))
# Email pattern
email_pattern = r'\b[A-Za-z0-9._%+-]+@[A-Za-z0-9.-]+\.[A-Z|a-z]{2,}\b'
iocs['email_addresses'] = list(set(re.findall(email_pattern, email_content)))
return iocs
Expected Deliverables
- Completed analysis reports for each phishing email
- IOC list with enrichment data
- YARA rules for future detection
- Updated incident response playbook
- Blog post documenting the process
Evaluation Criteria
- Accuracy of phishing identification
- Completeness of IOC extraction
- Quality of analysis reports
- Understanding of email security concepts
- Documentation quality
Extension Ideas
- Create automated phishing detection script
- Integrate with SIEM for real-time alerts
- Develop machine learning model for phishing detection
- Build phishing awareness training materials
Resources
- NIST SP 800-61 Computer Security Incident Handling Guide
- Phishing Email Analysis Techniques
- MITRE ATT&CK Framework
Safety Notes
- Always analyze attachments in isolated environment
- Never click suspicious links during analysis
- Use dedicated analysis workstation
- Follow organizational security policies