SOC Analyst Projects
- Jean-Christophe Miler
- Soc , Cybersecurity
- February 12, 2026
Table of Contents
Welcome to a comprehensive collection of hands-on SOC Analyst projects designed to build practical cybersecurity skills.
📁 Project Overview
This repository contains five detailed SOC Analyst projects covering essential security operations domains:
🔍 1. Phishing Email Analysis Lab
Focus: Email security and threat intelligence
- Analyze phishing emails and headers
- Extract indicators of compromise (IOCs)
- Build email security awareness
- Tools: Python, VirusTotal, YARA rules
🖥️ 2. Windows Log Forensics Investigation
Focus: Incident response and digital forensics
- Analyze Windows Event Logs
- Detect security incidents and intrusions
- Build attack timelines
- Tools: Event Viewer, Python, Hayabusa
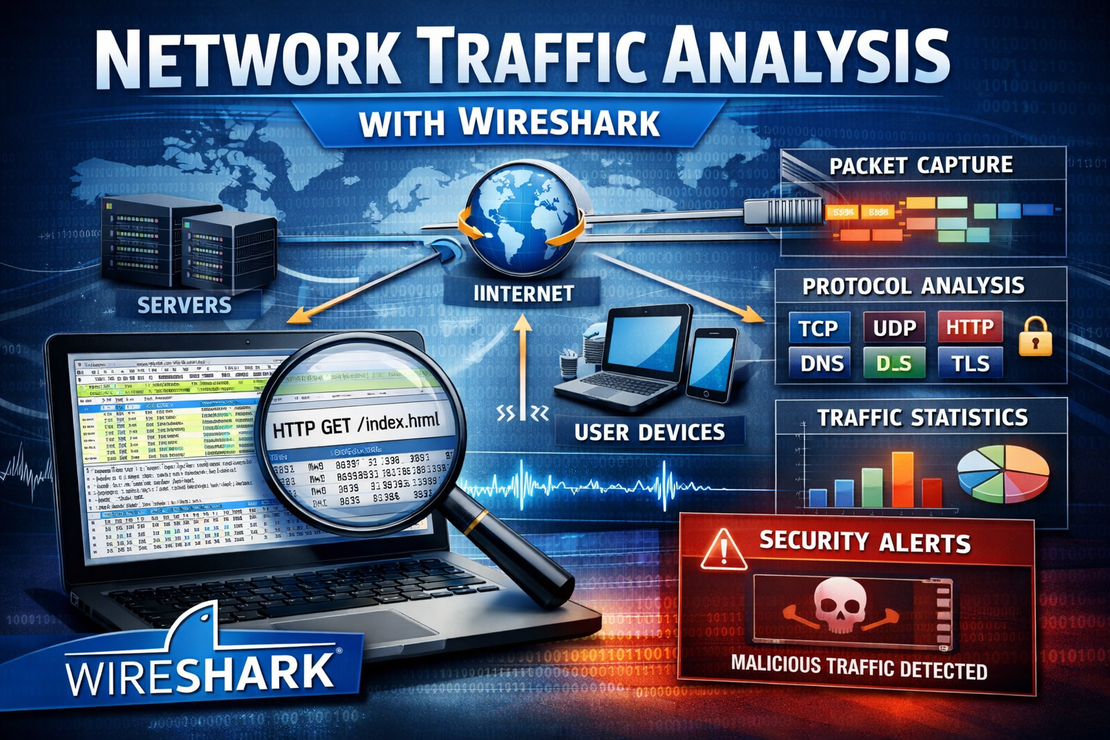
🌐 3. Network Traffic Analysis with Wireshark
Focus: Network security and traffic analysis
- Analyze malicious network patterns
- Detect C2 communications and data exfiltration
- Master packet-level investigation
- Tools: Wireshark, TShark, Scapy
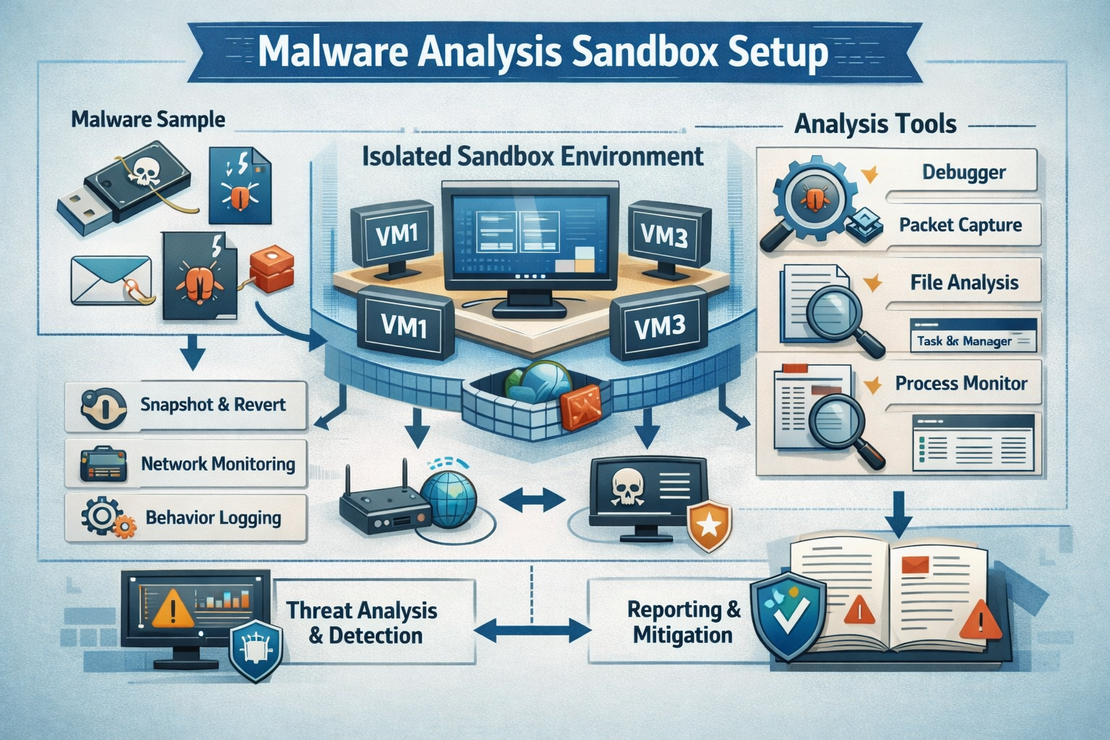
🛡️ 4. Malware Analysis Sandbox Setup
Focus: Reverse engineering and malware analysis
- Build secure analysis environment
- Perform static and dynamic analysis
- Extract behavioral IOCs
- Tools: VMware, Sysmon, YARA, Ghidra
📊 5. SIEM Rule Creation and Testing
Focus: Security monitoring and detection engineering
- Develop custom detection rules
- Test rule accuracy and performance
- Optimize for multiple SIEM platforms
- Tools: Splunk, Elastic Stack, Microsoft Sentinel
🎯 Learning Objectives
By completing these projects, you will gain expertise in:
Technical Skills
- Threat Detection: Identify and analyze various attack vectors
- Incident Response: Develop systematic response procedures
- Digital Forensics: Extract and analyze digital evidence
- Security Tools: Master industry-standard security tools
- Scripting: Automate security analysis with Python
Analytical Skills
- Pattern Recognition: Identify malicious behavior patterns
- Timeline Analysis: Reconstruct security incident chronology
- Risk Assessment: Evaluate and prioritize security threats
- Report Writing: Document findings professionally
Professional Development
- Blog Content: Generate technical blog posts
- Portfolio Building: Create demonstrable projects
- Interview Preparation: Practice common SOC scenarios
- Industry Knowledge: Understand security operations workflows
🛠️ Prerequisites
Required Software
- Python 3.8+ with security libraries
- Virtualization platform (VMware/VirtualBox)
- Network analysis tools (Wireshark)
- Log analysis tools (Event Viewer)
- Text editor/IDE
System Requirements
- 16GB+ RAM (for virtualization)
- 100GB+ free disk space
- Dedicated analysis workstation
- Isolated network environment
Knowledge Base
- Basic understanding of networking
- Windows operating system knowledge
- Fundamental security concepts
- Programming basics (Python preferred)
🚀 Getting Started
1. Project Selection
Choose projects based on your interests and current skill level:
| Skill Level | Recommended Projects |
|---|---|
| Beginner | 1. Phishing Email Analysis |
| Intermediate | 2. Windows Log Forensics, 3. Network Analysis |
| Advanced | 4. Malware Analysis, 5. SIEM Rule Creation |
2. Environment Setup
Follow the setup instructions in each project directory:
- Install required tools and dependencies
- Configure virtual machines and networks
- Prepare sample data and test cases
- Review safety procedures
3. Implementation Approach
For each project:
- Study the learning objectives
- Set up the analysis environment
- Follow the step-by-step instructions
- Complete the analysis tasks
- Document your findings
- Share via blog post
📈 Skill Progression Path
Week 1-2: Phishing Email Analysis
Week 3-4: Windows Log Forensics
Week 5-6: Network Traffic Analysis
Week 7-8: Malware Analysis Sandbox
Week 9-10: SIEM Rule Creation
Week 11-12: Integration Projects & Blog Writing
📝 Blog Content Ideas
Each project provides rich material for technical blog posts:
Content Types
- Tutorial Series: Step-by-step project implementation
- Tool Reviews: In-depth tool comparisons and tips
- Case Studies: Real-world incident analysis
- Best Practices: Security operations guidelines
- Career Development: SOC Analyst skill building
SEO-Friendly Topics
- “How to Set Up a Home Malware Analysis Lab”
- “Complete Guide to Windows Log Forensics”
- “Network Traffic Analysis for Beginners”
- “Building SIEM Rules That Actually Work”
- “SOC Analyst Skills You Need in 2026”
🔗 Integration Opportunities
Combine projects for comprehensive security scenarios:
Multi-Stage Attack Analysis
- Detect phishing email (Project 1)
- Analyze compromise evidence in logs (Project 2)
- Investigate network traffic patterns (Project 3)
- Analyze malware payload (Project 4)
- Create detection rules (Project 5)
Continuous Improvement Loop
- Use analysis findings to improve detection rules
- Update threat intelligence feeds
- Enhance monitoring capabilities
- Document lessons learned
📊 Expected Outcomes
Technical Deliverables
- 5 Complete Project Reports: Detailed analysis documentation
- 15+ Custom Scripts: Automation and analysis tools
- 25+ Detection Rules: SIEM-ready security rules
- Comprehensive IOC Lists: Threat intelligence data
- Blog Post Series: 5+ technical articles
Career Benefits
- Portfolio Enhancement: Demonstrable technical projects
- Interview Preparation: Real-world SOC scenarios
- Skill Certification: Practical experience evidence
- Industry Recognition: Published technical content
🛡️ Safety and Ethics
Security Considerations
- Isolated Environments: Never analyze malware on production systems
- Network Segmentation: Separate analysis from trusted networks
- Data Sanitization: Remove sensitive information before sharing
- Legal Compliance: Follow applicable laws and regulations
Ethical Guidelines
- Responsible Disclosure: Report vulnerabilities properly
- Privacy Protection: Handle personal data carefully
- Professional Conduct: Maintain industry standards
- Continuous Learning: Stay updated with security trends
📚 Additional Resources
Online Learning
Community Resources
Industry Frameworks
🤝 Contributing
Share your improvements and variations:
- Fork the repository
- Create feature branches
- Submit pull requests
- Document your enhancements
📄 License
This project collection is provided for educational purposes. Please ensure compliance with your organization’s policies and applicable laws when implementing these techniques.